Install PyKD in WinDbg
WinDbg is a Windows user- and kernel-mode debugger. It has a built-in scripting language, but I find it rather limited for exploit development. I’d much rather code in Python.
Thankfully, the Pykd extension lets us run Python scripts inside WinDbg!
Prerequisites
Before installing Pykd, you should have WinDbg and Python installed.
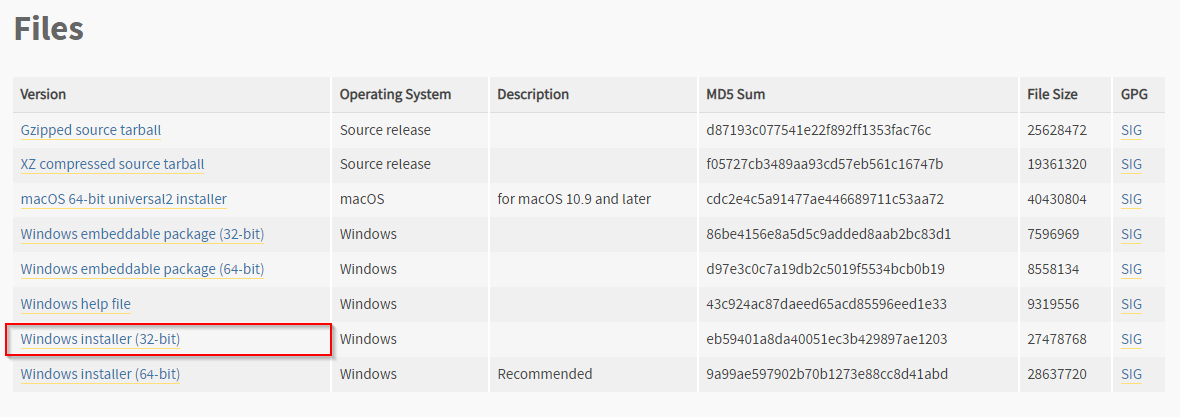
You can use either Python 2 or 3, but make sure that the architecture matches your WinDbg version. In my case, I am using x86 builds for everything.
- Download WinDbg: https://docs.microsoft.com/en-us/windows-hardware/drivers/debugger/debugger-download-tools
- Download Python: https://www.python.org/downloads/
Installing pykd.dll
Download the latest version of Pykd extension from the project GitLab repo:
https://githomelab.ru/pykd/pykd-ext/wikis/Downloads
Extract the folder. It contains two DLL versions: 32-bit (x86) and 64-bit (x64). Choose the version that matches your WinDbg application (in my case, that’s x86).
In order for WinDbg to find the DLL you need to do one of the following options:
- Place it in
C:\Program Files (x86)\Windows Kits\10\Debuggers\x86\winext, OR - Create a new working directory
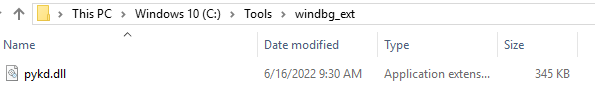
I prefer the second option since I can easily locate all my scripts and extensions. Here’s where I placed my pykd.dll file:
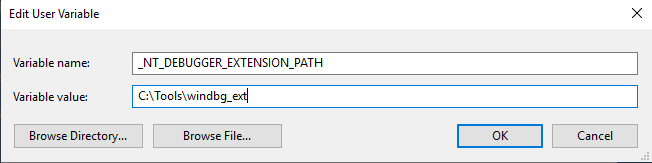
Now we need to tell WinDbg to look here for extensions. Update the NT_DEBUGGER_EXTENSION_PATH environment variable to set the default path for extension DLLs.
Install Pykd Python library
Now that the DLL is in place, we can install Pykd from a command prompt using pip:
pip install pykd
Using Pykd in WinDbg
Open WinDbg and attach it to a process (i.e. notepad.exe)
Load the Pykd extension:
.load pykd
Read the help documentation:
!help
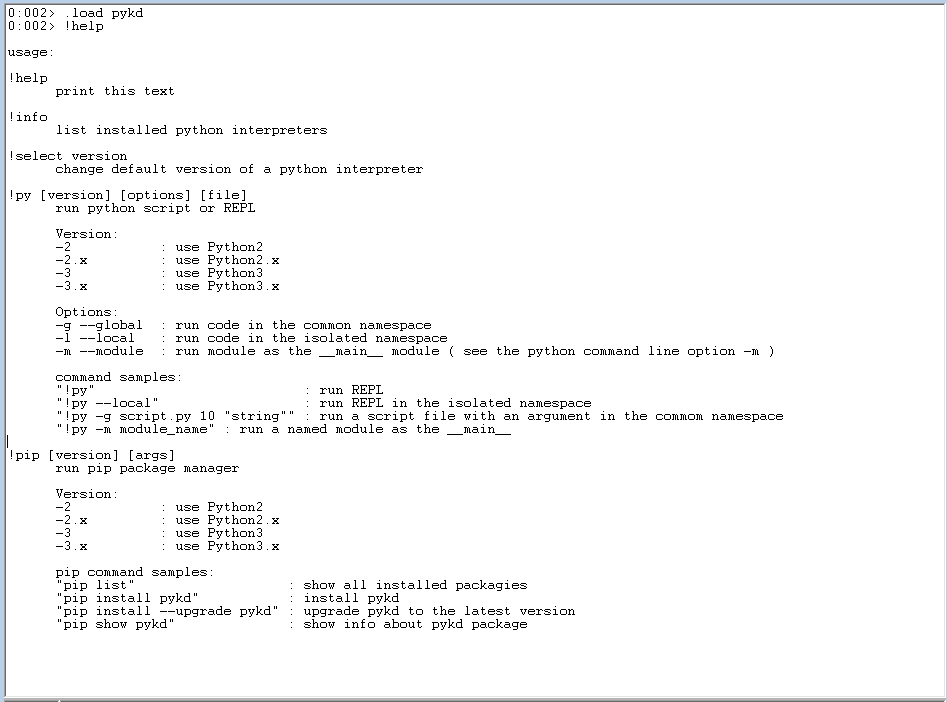
Invoke the Python interpreter:
!py
Running scripts
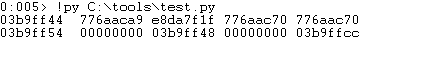
Below is a simple test script that displays 8 DWORDs from the stack
import pykd
print(pykd.dbgCommand("dd esp L8"))
And here’s the output in WinDbg:
Further Reading
If interested in exploit development, check out epi052’s scripts for OSED. They were created for the Windows Usermode Exploit Developer course, but are also useful IRL.